linux - composer 的SSL錯誤
問題描述
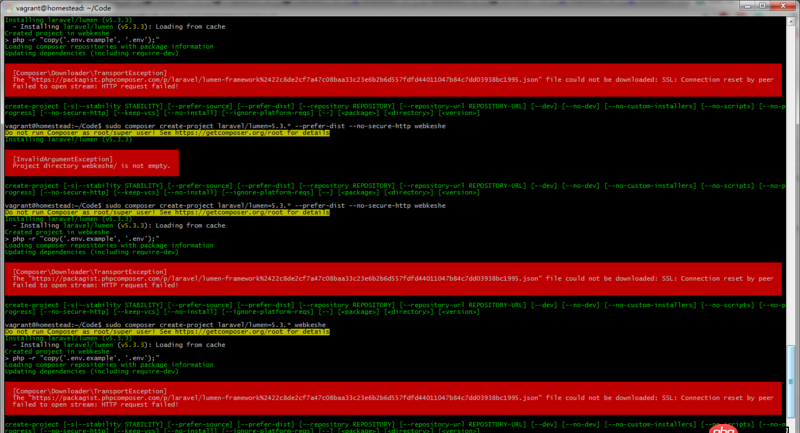
我用的是homestead 2.1.0,vagrant 1.9.2,composer用的是laravel-china的國內(nèi)源,composer時報這個錯誤,請問怎么回事,該如何解決?
[ComposerDownloaderTransportException] The 'https://packagist.phpcomposer.com/p/laravel/lumen-framework%2422c8de2cf7a47c08baa33c23e6b2b6d557fdfd44011047b84c7dd03938bc1995.json' file could not be downloaded: SSL: Connection reset by peer failed to open stream: HTTP request failed!
網(wǎng)上尋找解決方案無果
誰能解決支付寶轉(zhuǎn)賬一頓早餐錢酬謝!!!!!!!!!!!!
問題解答
回答1:https://packagist.phpcomposer.com/p/laravel/lumen-framework%2422c8de2cf7a47c08baa33c23e6b2b6d557fdfd44011047b84c7dd03938bc1995.json這個url可以訪問文件,你可以直接拷貝下來,在根目錄下命名為composer.json,再重新執(zhí)行
回答2:先檢查你的php是否安裝了openssl,如果安裝了還報錯,在C:usrlocalssl建立openssl.cnf,內(nèi)容如下,這是NT版本編譯寫死的路徑。
## OpenSSL example configuration file.# This is mostly being used for generation of certificate requests.## This definition stops the following lines choking if HOME isn’t# defined.HOME = .RANDFILE= $ENV::HOME/.rnd# Extra OBJECT IDENTIFIER info:#oid_file= $ENV::HOME/.oidoid_section= new_oids# To use this configuration file with the '-extfile' option of the# 'openssl x509' utility, name here the section containing the# X.509v3 extensions to use:# extensions= # (Alternatively, use a configuration file that has only# X.509v3 extensions in its main [= default] section.)[ new_oids ]# We can add new OIDs in here for use by ’ca’, ’req’ and ’ts’.# Add a simple OID like this:# testoid1=1.2.3.4# Or use config file substitution like this:# testoid2=${testoid1}.5.6# Policies used by the TSA examples.tsa_policy1 = 1.2.3.4.1tsa_policy2 = 1.2.3.4.5.6tsa_policy3 = 1.2.3.4.5.7####################################################################[ ca ]default_ca = CA_default# The default ca section####################################################################[ CA_default ]dir= ./demoCA# Where everything is keptcerts= $dir/certs# Where the issued certs are keptcrl_dir= $dir/crl# Where the issued crl are keptdatabase = $dir/index.txt # database index file.#unique_subject = no # Set to ’no’ to allow creation of # several ctificates with same subject.new_certs_dir = $dir/newcerts# default place for new certs.certificate = $dir/cacert.pem # The CA certificateserial= $dir/serial # The current serial numbercrlnumber = $dir/crlnumber # the current crl number # must be commented out to leave a V1 CRLcrl= $dir/crl.pem # The current CRLprivate_key = $dir/private/cakey.pem# The private keyRANDFILE = $dir/private/.rand # private random number filex509_extensions = usr_cert# The extentions to add to the cert# Comment out the following two lines for the 'traditional'# (and highly broken) format.name_opt = ca_default# Subject Name optionscert_opt = ca_default# Certificate field options# Extension copying option: use with caution.# copy_extensions = copy# Extensions to add to a CRL. Note: Netscape communicator chokes on V2 CRLs# so this is commented out by default to leave a V1 CRL.# crlnumber must also be commented out to leave a V1 CRL.# crl_extensions = crl_extdefault_days = 365 # how long to certify fordefault_crl_days= 30 # how long before next CRLdefault_md = default# use public key default MDpreserve = no # keep passed DN ordering# A few difference way of specifying how similar the request should look# For type CA, the listed attributes must be the same, and the optional# and supplied fields are just that :-)policy= policy_match# For the CA policy[ policy_match ]countryName= matchstateOrProvinceName = matchorganizationName = matchorganizationalUnitName = optionalcommonName= suppliedemailAddress= optional# For the ’anything’ policy# At this point in time, you must list all acceptable ’object’# types.[ policy_anything ]countryName= optionalstateOrProvinceName = optionallocalityName= optionalorganizationName = optionalorganizationalUnitName = optionalcommonName= suppliedemailAddress= optional####################################################################[ req ]default_bits= 2048default_keyfile = privkey.pemdistinguished_name = req_distinguished_nameattributes= req_attributesx509_extensions = v3_ca # The extentions to add to the self signed cert# Passwords for private keys if not present they will be prompted for# input_password = secret# output_password = secret# This sets a mask for permitted string types. There are several options. # default: PrintableString, T61String, BMPString.# pkix : PrintableString, BMPString (PKIX recommendation before 2004)# utf8only: only UTF8Strings (PKIX recommendation after 2004).# nombstr : PrintableString, T61String (no BMPStrings or UTF8Strings).# MASK:XXXX a literal mask value.# WARNING: ancient versions of Netscape crash on BMPStrings or UTF8Strings.string_mask = utf8only# req_extensions = v3_req # The extensions to add to a certificate request[ req_distinguished_name ]countryName = Country Name (2 letter code)countryName_default= AUcountryName_min = 2countryName_max = 2stateOrProvinceName= State or Province Name (full name)stateOrProvinceName_default = Some-StatelocalityName = Locality Name (eg, city)0.organizationName= Organization Name (eg, company)0.organizationName_default = Internet Widgits Pty Ltd# we can do this but it is not needed normally :-)#1.organizationName= Second Organization Name (eg, company)#1.organizationName_default = World Wide Web Pty LtdorganizationalUnitName= Organizational Unit Name (eg, section)#organizationalUnitName_default =commonName = Common Name (e.g. server FQDN or YOUR name)commonName_max = 64emailAddress = Email AddressemailAddress_max= 64# SET-ex3 = SET extension number 3[ req_attributes ]challengePassword= A challenge passwordchallengePassword_min= 4challengePassword_max= 20unstructuredName= An optional company name[ usr_cert ]# These extensions are added when ’ca’ signs a request.# This goes against PKIX guidelines but some CAs do it and some software# requires this to avoid interpreting an end user certificate as a CA.basicConstraints=CA:FALSE# Here are some examples of the usage of nsCertType. If it is omitted# the certificate can be used for anything *except* object signing.# This is OK for an SSL server.# nsCertType = server# For an object signing certificate this would be used.# nsCertType = objsign# For normal client use this is typical# nsCertType = client, email# and for everything including object signing:# nsCertType = client, email, objsign# This is typical in keyUsage for a client certificate.# keyUsage = nonRepudiation, digitalSignature, keyEncipherment# This will be displayed in Netscape’s comment listbox.nsComment = 'OpenSSL Generated Certificate'# PKIX recommendations harmless if included in all certificates.subjectKeyIdentifier=hashauthorityKeyIdentifier=keyid,issuer# This stuff is for subjectAltName and issuerAltname.# Import the email address.# subjectAltName=email:copy# An alternative to produce certificates that aren’t# deprecated according to PKIX.# subjectAltName=email:move# Copy subject details# issuerAltName=issuer:copy#nsCaRevocationUrl= http://www.domain.dom/ca-crl.pem#nsBaseUrl#nsRevocationUrl#nsRenewalUrl#nsCaPolicyUrl#nsSslServerName# This is required for TSA certificates.# extendedKeyUsage = critical,timeStamping[ v3_req ]# Extensions to add to a certificate requestbasicConstraints = CA:FALSEkeyUsage = nonRepudiation, digitalSignature, keyEncipherment[ v3_ca ]# Extensions for a typical CA# PKIX recommendation.subjectKeyIdentifier=hashauthorityKeyIdentifier=keyid:always,issuer# This is what PKIX recommends but some broken software chokes on critical# extensions.#basicConstraints = critical,CA:true# So we do this instead.basicConstraints = CA:true# Key usage: this is typical for a CA certificate. However since it will# prevent it being used as an test self-signed certificate it is best# left out by default.# keyUsage = cRLSign, keyCertSign# Some might want this also# nsCertType = sslCA, emailCA# Include email address in subject alt name: another PKIX recommendation# subjectAltName=email:copy# Copy issuer details# issuerAltName=issuer:copy# DER hex encoding of an extension: beware experts only!# obj=DER:02:03# Where ’obj’ is a standard or added object# You can even override a supported extension:# basicConstraints= critical, DER:30:03:01:01:FF[ crl_ext ]# CRL extensions.# Only issuerAltName and authorityKeyIdentifier make any sense in a CRL.# issuerAltName=issuer:copyauthorityKeyIdentifier=keyid:always[ proxy_cert_ext ]# These extensions should be added when creating a proxy certificate# This goes against PKIX guidelines but some CAs do it and some software# requires this to avoid interpreting an end user certificate as a CA.basicConstraints=CA:FALSE# Here are some examples of the usage of nsCertType. If it is omitted# the certificate can be used for anything *except* object signing.# This is OK for an SSL server.# nsCertType = server# For an object signing certificate this would be used.# nsCertType = objsign# For normal client use this is typical# nsCertType = client, email# and for everything including object signing:# nsCertType = client, email, objsign# This is typical in keyUsage for a client certificate.# keyUsage = nonRepudiation, digitalSignature, keyEncipherment# This will be displayed in Netscape’s comment listbox.nsComment = 'OpenSSL Generated Certificate'# PKIX recommendations harmless if included in all certificates.subjectKeyIdentifier=hashauthorityKeyIdentifier=keyid,issuer# This stuff is for subjectAltName and issuerAltname.# Import the email address.# subjectAltName=email:copy# An alternative to produce certificates that aren’t# deprecated according to PKIX.# subjectAltName=email:move# Copy subject details# issuerAltName=issuer:copy#nsCaRevocationUrl= http://www.domain.dom/ca-crl.pem#nsBaseUrl#nsRevocationUrl#nsRenewalUrl#nsCaPolicyUrl#nsSslServerName# This really needs to be in place for it to be a proxy certificate.proxyCertInfo=critical,language:id-ppl-anyLanguage,pathlen:3,policy:foo####################################################################[ tsa ]default_tsa = tsa_config1 # the default TSA section[ tsa_config1 ]# These are used by the TSA reply generation only.dir= ./demoCA# TSA root directoryserial= $dir/tsaserial # The current serial number (mandatory)crypto_device = builtin# OpenSSL engine to use for signingsigner_cert = $dir/tsacert.pem # The TSA signing certificate # (optional)certs= $dir/cacert.pem # Certificate chain to include in reply # (optional)signer_key = $dir/private/tsakey.pem # The TSA private key (optional)default_policy = tsa_policy1# Policy if request did not specify it # (optional)other_policies = tsa_policy2, tsa_policy3 # acceptable policies (optional)digests= md5, sha1# Acceptable message digests (mandatory)accuracy = secs:1, millisecs:500, microsecs:100 # (optional)clock_precision_digits = 0 # number of digits after dot. (optional)ordering= yes # Is ordering defined for timestamps?# (optional, default: no)tsa_name= yes # Must the TSA name be included in the reply?# (optional, default: no)ess_cert_id_chain = no # Must the ESS cert id chain be included?# (optional, default: no)回答3:
我覺得你可以換一個源試試,比如http://www.phpcomposer.com
回答4:是這樣的, composer升級以后需要必須使用https,但是可以通過配置進(jìn)行支持http,也就是在,config.json中配置`
{ 'config': {'secure-http': false }}
`
相關(guān)文章:
1. javascript - immutable配合react提升性能?2. javascript - sublime快鍵鍵問題3. phpstudy8.1支持win11系統(tǒng)嗎?4. javascript - 移動端上不能實(shí)現(xiàn)拖拽布局嗎?5. vue.js - Vue 如何像Angular.js watch 一樣監(jiān)聽數(shù)據(jù)變化6. 實(shí)現(xiàn)bing搜索工具urlAPI提交7. 配置Apache時,添加對PHP的支持時語法錯誤8. Apache 已經(jīng)把網(wǎng)站根目錄的改為allow from all了,但是服務(wù)器還是不能訪問?9. css - 寫頁面遇到個布局問題,求大佬們幫解答,在線等,急!~10. javascript - nodejs關(guān)于進(jìn)程間發(fā)送句柄的一點(diǎn)疑問

 網(wǎng)公網(wǎng)安備
網(wǎng)公網(wǎng)安備